Navigating the world of Department of Defense (DoD) contracts can feel like learning a new language, and CMMC is one of its most important dialects. A CMMC compliance service is your expert translator and guide, helping you meet the strict Cybersecurity Maturity Model Certification (CMMC) rules.
Think of it as hiring a specialized architect. You wouldn’t build a federal facility without someone who knows the government’s unique building codes, right? It’s the same for your digital infrastructure—a CMMC service ensures your data security is built to the DoD's exacting standards, a crucial step for winning and keeping those valuable contracts.
Why Your DoD Contract Depends on CMMC Compliance
If your business is part of the Defense Industrial Base (DIB), let's be crystal clear: CMMC compliance isn't just a good idea; it's a non-negotiable requirement for staying in business. The DoD has drawn a line in the sand. If you handle sensitive government information, you must prove your cybersecurity is up to snuff. Simply hoping for the best is no longer a strategy.
The building code analogy really hits home here. CMMC acts as a specialized code for your company's digital walls and vaults. If you can't get the certificate that proves you've met these codes, you're not allowed on the job site. This has been a massive wake-up call, especially for small and mid-sized businesses (SMBs) that often don't have a dedicated team to untangle this complex framework.
The Clock Is Ticking
The CMMC rollout has uncovered a serious readiness gap across the industry. Here's a number that should get your attention: a recent study found that only 1% of DIB contractors are actually ready for their assessments. That’s a staggering figure, and it highlights just how urgently companies need expert help, especially with enforcement already in motion. You can dig into the full research on contractor readiness from the 2025 State of the DIB Report to see the full scope of the issue.
For most SMBs, trying to decipher and implement hundreds of security controls on their own is a recipe for frustration and failure. This is precisely where a CMMC compliance service proves its worth, acting as your partner to turn dense regulations into a clear, step-by-step plan.
A CMMC compliance service doesn't just hand you a to-do list. They roll up their sleeves and help you build, document, and prove your security program is sound. They're the difference between hoping you’re ready for an audit and knowing you are.
Understanding the CMMC 2.0 Levels
The DoD knows that not all information is created equal, so they designed a tiered system to match the security requirements to the sensitivity of the data you handle. The specific level you need to achieve will be written right into your DoD contracts. A good compliance partner will first help you pinpoint your target level and then map out the most efficient path to get there.
To help you get your bearings, here’s a quick overview of the three levels in CMMC 2.0.
CMMC 2.0 Levels at a Glance
This table breaks down the three CMMC 2.0 levels, who they apply to, and the assessment requirements for each.
| CMMC Level | Applies To | Assessment Type | Core Requirement |
|---|---|---|---|
| Level 1 (Foundational) | Contractors handling only Federal Contract Information (FCI). | Annual Self-Assessment | Implements 15 basic safeguarding requirements from FAR 52.204-21. |
| Level 2 (Advanced) | Contractors handling Controlled Unclassified Information (CUI). | Triennial Third-Party Assessment (for most) | Implements all 110 security controls from NIST SP 800-171. |
| Level 3 (Expert) | Contractors handling high-priority CUI programs. | Triennial Government-Led Assessment | Implements controls from NIST SP 800-171 plus a subset of NIST SP 800-172. |
Each level builds on the last, with requirements becoming more stringent as the data's sensitivity increases.
Bringing in a CMMC compliance service transforms this overwhelming process into a manageable project. It's a strategic investment to ensure you aren't shut out of future DoD opportunities and can bid on contracts with the confidence that your cybersecurity meets the government's unyielding standards.
What a CMMC Compliance Service Actually Delivers
When you hear “CMMC compliance service,” it can sound a bit vague. What do you actually get?
Think of it less like a subscription and more like hiring a specialized construction crew. Their job is to build your company’s cybersecurity program from the ground up, following the DoD’s strict blueprints. They don't just hand you a complicated checklist and walk away.
A real compliance partner rolls up their sleeves and gets to work, becoming a true extension of your team. Their entire goal is to take the 110 controls of CMMC Level 2 and turn that intimidating list into a finished, auditable system. They make it a manageable project, not a total nightmare.
The Cybersecurity Health Check or Gap Analysis
The very first thing you’ll get is a Gap Analysis. This is your cybersecurity "health check."
This process meticulously compares every part of your current IT setup against every single CMMC requirement. It’s all designed to answer one simple question: "Where are we today, and where do we need to be?"
Your partner will look at everything—from how your team logs into their computers to how you back up company data. They’ll review your network, your cloud services, and any policies you might already have. What you get back is a detailed report that clearly flags every control you meet, partially meet, or don't meet at all.
Practical Example: A gap analysis might discover your team uses a shared login for a key software tool. That’s an immediate failure of CMMC’s unique user ID control (IA.L2-3.5.1). The report would flag this as a critical gap and provide an actionable recommendation, such as: "Create individual named user accounts for all staff in the CAD software and disable the 'engineer' shared account by March 31st."
The Prioritized Remediation Plan
Once all the gaps are out in the open, the next step is creating a Remediation Plan. This isn't just a laundry list of problems; it’s a smart, prioritized project plan for fixing them.
Your CMMC provider will organize all the required fixes based on cost, effort, and security impact. Suddenly, you have a logical, step-by-step roadmap to get you to the finish line. This is where a mountain of issues gets broken down into a series of manageable molehills. Instead of staring down 110 controls, you get a clear guide.
- Priority 1 Task: Turn on multi-factor authentication (MFA) for all Microsoft 365 accounts to satisfy control IA.L2-3.5.3. This is a huge win for security with a relatively low cost.
- Priority 2 Task: Write up an incident response plan and run a practice drill (a "tabletop exercise") to meet IR.L2-3.6.1. This is more about process and documentation.
- Priority 3 Task: Encrypt all company laptops to protect Controlled Unclassified Information (CUI) when it's just sitting there, which addresses control SC.L2-3.13.16.
This approach gives you a clear path forward, letting you knock out the most critical items first. Having a structured process is absolutely vital, especially since recent analysis shows that over 60% of DIB organizations find CMMC compliance very difficult to handle on their own.
Hands-On Implementation and Evidence Collection
Here’s where a true partner really shines. They don’t stop at just planning. The best CMMC compliance services provide hands-on help with Remediation and Implementation.
They won't just tell you to “implement MFA”—they will actually help you configure it. They won't just say “write a policy”—they will help you draft it based on proven templates.
At the same time, they start building your body of evidence. For CMMC, you can’t just be compliant; you have to prove it. Your partner will be grabbing screenshots, exporting configuration files, and documenting every process along the way. All this evidence gets neatly organized for the C3PAO (the official auditor) when assessment day comes.
This hands-on support is exactly why partnering with an MSP can be a game-changer for conquering compliance.
Building Your CMMC Governance and Documentation
Most business owners think CMMC compliance is all about fancy new firewalls and complex security software. While technology is a huge piece of the puzzle, it's only half the battle. The other half—the part that trips up most companies—is all about governance and documentation.
Think of it like building a custom-designed vault. The thick steel door and sophisticated lock are your tech controls. But when the auditor shows up, they don't just want to see the vault. They want to see the logbook detailing who accessed it and when, the written policy on who gets the combination, and the procedure for what happens if it's compromised.
Without that paper trail, your security is just an opinion. CMMC requires you to prove it.
The Two Documents That Matter Most
A huge part of what a CMMC compliance service does is build that paper trail for you. They save you from staring at a blank page by drafting, refining, and managing two of the most foundational documents in the entire CMMC process: the System Security Plan (SSP) and the Plan of Action & Milestones (POA&M).
Don't mistake these for bureaucratic busywork. These two documents are the heart of your entire compliance effort and will be the very first things an assessor asks to see.
- System Security Plan (SSP): This is the official blueprint for your entire security program. It’s a detailed guide that explains exactly how your company meets every single one of the 110 security controls required for CMMC Level 2.
- Plan of Action & Milestones (POA&M): Think of this as your project plan or renovation to-do list. It identifies any security gaps you currently have and lays out a concrete plan to fix them, including what needs to be done, who’s responsible, and by when.
An experienced CMMC partner doesn’t just hand you a generic template. They work with you to translate your real-world business and IT operations into the specific, structured language that CMMC assessors need to see.
Practical Example: Let's say your company uses a firewall to protect your network. A good SSP won't just say "we have a firewall." It will specify the exact make and model (e.g., "FortiGate 60F"), detail the specific rule sets that block unwanted traffic, and point to the written policy (e.g., "AC-P-01, Access Control Policy") that governs how those rules are managed—ticking the boxes for multiple CMMC controls at once.
Why Documentation Is a Major Sticking Point
Creating and maintaining this level of documentation is where so many businesses get stuck. It’s an incredibly time-consuming and meticulous process. For small and mid-sized businesses that don't have a full-time compliance officer, it can feel completely overwhelming.
The data backs this up. Recent research shows that governance failures are a massive roadblock, tripping up 62% of DoD contractors trying to achieve CMMC 2.0 Level 2. The same study revealed that a staggering 64% of companies don't even have a complete System Security Plan (SSP)—the most basic foundational document. You can see all the findings and learn more about the governance challenges facing DoD suppliers from Kiteworks' 2025 survey.
This is precisely the gap a CMMC compliance service is designed to fill. They bring the right templates, deep expertise, and dedicated man-hours to the table. They ensure your SSP and POA&M are not just complete but actually reflect your security posture, saving your team hundreds of hours and preventing the common errors that lead to a failed assessment. By handling the paperwork, they let you get back to running your business.
Securing Your Microsoft 365 for CMMC Compliance
If you're like most businesses we work with, Microsoft 365 isn't just for email—it's the central hub where all the work gets done. That makes securing it a top priority for any CMMC compliance service. But there’s a huge misconception we see all the time: just having Microsoft 365 doesn't make you compliant.
Microsoft gives you an incredibly powerful and secure platform, but it’s best to think of it as a professional-grade workshop full of tools. The tools are all there, but you are responsible for using them correctly to build something that meets CMMC standards. It doesn't happen on its own; it takes deliberate setup and ongoing management.

Turning on the Right Security Features
A hands-on CMMC partner will roll up their sleeves and dive right into your Microsoft 365 admin centers. Our job is to configure the specific settings that CMMC auditors are trained to look for. This isn't about selling you new products; it's about activating and fine-tuning the powerful features you probably already own, especially if you have a license like Microsoft 365 Business Premium.
Here are a few real-world examples of what that actually looks like:
- Implementing Data Loss Prevention (DLP) Policies: An actionable step is to create a rule that automatically scans outgoing emails. If it spots an attachment that looks like a technical drawing or has a CUI label, it can block the email and alert a security officer. This is a practical way to stop accidental data leaks, a major CMMC concern.
- Enabling Specific Audit Logs: CMMC demands you know who accessed sensitive data and when. A partner will make sure the right audit logs in Microsoft Purview are switched on and set to keep records for at least 90 days. This creates the digital paper trail you absolutely need for an assessment.
- Using Information Protection and Encryption: A compliance service can configure Azure Information Protection to automatically label and encrypt any document saved to a specific SharePoint site, like one named "CUI-Projects." This means that even if someone downloads a file to their laptop, it stays encrypted and unreadable to anyone without permission.
These technical settings are where the rubber meets the road, turning CMMC rules from words on a page into real, active protection. For a closer look at these tools, you might find our guide on Microsoft 365 Business Premium tools your business should know about helpful.
Commercial vs GCC High Explained
As you move further down the CMMC path, you’ll hit a major crossroads: is your standard Microsoft 365 "Commercial" environment enough, or do you need to migrate to the more secure "GCC High" government cloud? This is a critical decision, as a migration can be expensive and disruptive.
Think of it this way: Microsoft 365 Commercial is like a modern, secure bank branch that’s open to the public. In contrast, GCC High is like a fortified vault located on a military base.
The key difference really boils down to data sovereignty and personnel screening. GCC High guarantees that all your data is stored within the continental U.S. and is only managed by screened U.S. persons. The standard Commercial version simply can't offer those same guarantees.
So, when is the expensive and complicated move to GCC High actually necessary?
- You Handle Export-Controlled Data (ITAR/EAR): If your contract involves technical data controlled by the International Traffic in Arms Regulations (ITAR) or Export Administration Regulations (EAR), GCC High is almost always a requirement. These regulations are incredibly strict about who can access the data, and the Commercial cloud can't meet that bar.
- Your Contract Demands It: Some DoD contracts will spell it out for you, requiring that all work be performed in a cloud environment that meets specific security levels (like DoD SRG IL4) or has compliance reports that only GCC High can provide.
This is where a knowledgeable CMMC partner provides enormous value. We analyze your specific contracts and the type of data you handle to give you a clear, risk-based recommendation. We can help you figure out if you can safely meet CMMC Level 2 in your current Commercial setup or if the move to GCC High is truly unavoidable for your business.
How to Choose the Right CMMC Partner in North Carolina
Picking a partner for your CMMC compliance journey is a massive decision, especially for a small or mid-sized business where every dollar has to count. The right CMMC compliance service can make this complex process feel smooth and successful. But the wrong one? That can lead to wasted time, a trashed budget, and a failed assessment that jeopardizes your DoD contracts.
Think of it like hiring a general contractor to build your dream home. You wouldn’t just hire someone because they have a flashy truck and a slick sales pitch. You’d want to see their portfolio, talk to past clients, and check their credentials. The same exact logic applies here—you have to vet your CMMC partner like your business depends on it, because it does.
Go Beyond the Sales Pitch with Telling Questions
Anyone can slap "CMMC Expert" on their website. Your job is to tell the difference between the real-deal experts and the opportunists who just showed up to the party. The best way to do that is to ask pointed, evidence-based questions that cut right through the marketing fluff.
Don’t just ask if they have experience. Ask them to prove it. A seasoned CMMC provider will be ready for these questions and will have confident, clear answers. How they respond—or if they can’t respond at all—will tell you everything you need to know.
A truly qualified CMMC compliance service won't just tell you what they do; they will be able to show you. They should have no problem providing sanitized, real-world examples of their work and explaining exactly how they get clients ready for the pressure of a live assessment.
Here are a few powerful questions you should absolutely have on your vetting checklist:
- Can you show me a sanitized SSP and POA&M you've created for a company like mine? This is the ultimate gut check. It proves they’ve been in the trenches and can produce the kind of detailed, high-quality documents that assessors scrutinize.
- Are you a Cyber AB Registered Provider Organization (RPO)? This is non-negotiable. An RPO designation means the organization has been officially vetted by the CMMC Accreditation Body (the Cyber AB) and follows their code of conduct. It's a basic, fundamental credential.
- How, specifically, will you prepare our team for the C3PAO assessment? A great partner does more than just plug technical holes. They should be running mock interviews, conducting readiness drills, and coaching your team on how to answer an auditor's questions with confidence and precision.
Choosing the right provider is a critical step in your compliance process. It's important to ask the right questions to ensure you're partnering with an organization that has the right expertise and is a good fit for your business.
To help you with this, we've put together a checklist of key criteria to consider when evaluating potential CMMC compliance service providers.
Vendor Selection Checklist
| Criteria | What to Ask | Why It Matters |
|---|---|---|
| CMMC-Specific Credentials | Are you a Cyber AB RPO? Do you have Registered Practitioners (RPs) or Certified Professionals (CPs) on staff? | This is the baseline. Official registration shows they are vetted by the CMMC governing body and are serious about compliance. |
| Demonstrable Experience | Can you show me a sanitized example of an SSP or POA&M you’ve created? | Talk is cheap. This is direct proof they can produce the detailed documentation required for an assessment. |
| Assessment Preparation | What is your process for mock assessments? How do you prepare our team for interviews with the C3PAO? | Technical compliance is only half the battle. Your team needs to be prepared to answer questions and demonstrate processes confidently. |
| Industry Specialization | Have you worked with other manufacturers (or your specific industry) in the DoD supply chain? | A provider who understands the nuances of your industry will be more efficient and effective than a generalist. |
| Tooling & Technology | What specific tools do you use for gap analysis, monitoring, and evidence collection? | This reveals their technical maturity. You want a partner who uses modern, efficient tools, not just spreadsheets and wishful thinking. |
| Local Presence (NC) | Do you have technicians who can provide on-site support in North Carolina if needed? | For complex hardware or network issues, having a local expert who can be physically present is a game-changer. |
| Long-Term Partnership | How do you support clients after the assessment for continuous monitoring and improvement? | CMMC isn't a one-and-done project. You need a partner who is in it for the long haul to help you maintain compliance. |
Using this checklist will give you a structured way to compare providers and make a much more informed decision. Don't be afraid to dig deep; a true partner will appreciate your diligence.
The Value of a Local North Carolina Partner
While a lot of CMMC work can happen remotely, there's a real, tangible value in having a partner who understands the business environment right here in North Carolina. A local Managed Service Provider (MSP) that also offers CMMC services brings a powerful combination of technical skill and local commitment.
A local provider is more than just another vendor—they're your neighbor. They get the specific challenges and opportunities for businesses across the state, from the Research Triangle to the industrial corridors. That local context can make a huge difference.
Think about these benefits of a North Carolina-based partner:
- On-Site Support: When you have a tricky issue with a server or a network switch, having an expert who can drive over and fix it is invaluable. Remote support is fantastic, but some problems just get solved faster in person.
- Long-Term Relationship: A local MSP isn't just looking for a one-off project. They want to be your trusted IT partner for years, helping you align your technology with your business goals long after your CMMC assessment is complete.
- Regional Understanding: They know the local labor market, the regional supply chains, and other factors unique to North Carolina that can influence your compliance strategy.
Choosing the right provider is a critical first step. For more general advice on what to look for, check out our guide on how to choose a managed service provider.
Mapping Your CMMC Timeline and Budget
It’s the first question on every business owner’s mind when they face a CMMC mandate: "How long is this going to take, and what’s it going to cost me?"
The honest-to-goodness answer is… it depends. There’s no single price tag because CMMC is a marathon, not a sprint, and your budget is tied directly to your starting line.
Think of it like a home renovation. The bill for a full gut-and-remodel of a kitchen is a world apart from just repainting the cabinets. A CMMC compliance service helps you scope that project, but a few key factors will always drive the final cost.
Unpacking the Key Cost Drivers
Instead of trying to pull a number out of thin air, it’s much more helpful to understand what actually moves the needle on your total investment. The cost and timeline for your CMMC journey really come down to three things.
- Your Starting Point: How big is your current security gap? A company that has already put in the work on NIST 800-171 controls is in a much better spot than one starting from absolute zero.
- Company Size and Complexity: A 20-person shop with a simple network has a much smaller lift than a 200-person firm with multiple locations and tangled legacy systems. More people, data, and systems means more work.
- Technology Needs: Will you need new software, like an advanced endpoint protection tool? Do you need to migrate your team to the ultra-secure Microsoft 365 GCC High environment? These technology investments can be major cost drivers.
Working with a CMMC partner makes these costs predictable. We can bundle services, find ways to use the tools you already have, and map out a phased approach that makes the investment manageable over time instead of hitting you with one massive upfront bill.
A Phased Approach to CMMC Implementation
Getting to CMMC Level 2 certification is a project, and it typically takes about a year to do it right. It's a structured process we break into distinct phases, each with its own clear goals and milestones. A good partner will walk you through every stage so nothing gets missed.
This graphic lays out a pretty standard twelve-month roadmap for getting CMMC-ready. It’s broken down into three manageable phases.
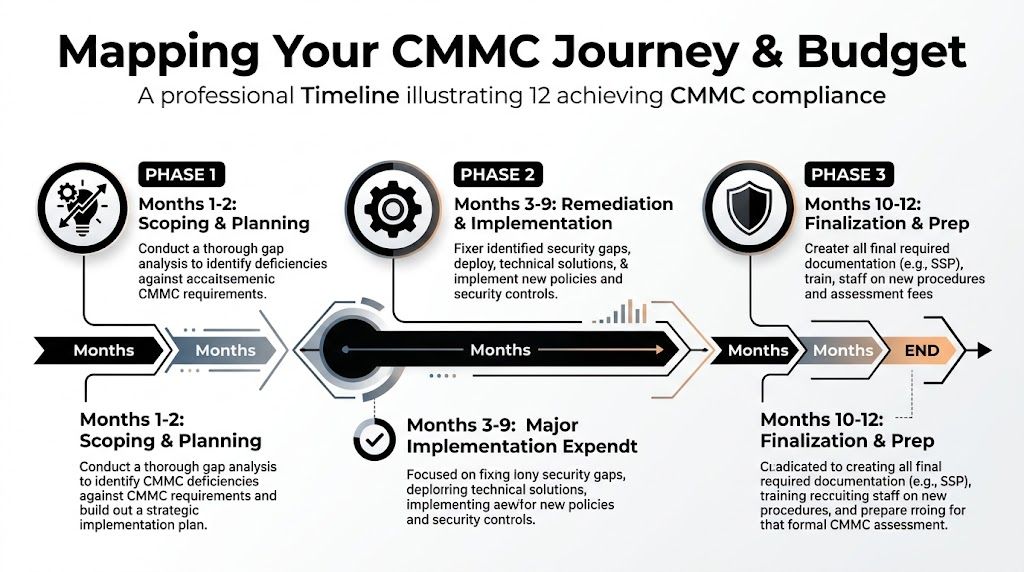
As you can see, this is a methodical journey, not a quick fix. The bulk of the hands-on work really kicks into gear during the middle months.
Here’s a closer look at what happens in each phase:
Months 1-2: Scoping and Strategic Planning
This first stage is all about discovery. We conduct a thorough gap analysis to pinpoint every single area where you fall short of the 110 controls. The result is a detailed System Security Plan (SSP) and a Plan of Action & Milestones (POA&M)—this becomes your strategic roadmap for the entire project.Months 3-9: Remediation and Implementation
This is where the heavy lifting happens. We get in the trenches with your team to fix the gaps we found earlier. It’s a mix of hands-on technical work, like configuring security settings, rolling out new tools, and drafting the required policies and procedures.Months 10-12: Finalization and Assessment Prep
In the home stretch, the focus shifts to proving your compliance. We work with you to gather evidence for every control, train your staff on new security policies, and run mock assessments. The goal is to make sure your team is completely prepared for the official C3PAO audit with no surprises.
Common Questions About CMMC Compliance Services
Even with a solid plan in place, the road to CMMC compliance can be filled with questions. We get it. We've talked with countless business owners about these very same concerns. Let's break down some of the most common questions we hear from companies looking for a CMMC compliance service.
Do We Still Need CMMC Level 2 for a Tiny Amount of CUI?
Yes, you do. This is a big one we see all the time. The need for CMMC Level 2 isn't about how much Controlled Unclassified Information (CUI) you handle, but whether you handle it at all. If your work for the DoD involves touching CUI in any way—creating it, storing it, or sending it—you're required to get certified at Level 2.
There's no "almost compliant" or a free pass for small amounts. Your very first step should always be a thorough gap analysis from a qualified CMMC compliance service. We can help you confirm exactly what data you have and what your true obligations are.
Can We Just Do CMMC Compliance Ourselves to Save Money?
While the DIY approach might seem like a good way to cut costs upfront, it's a risky path that often ends up being far more expensive. The CMMC framework isn't a simple checklist; it involves 110 specific technical controls, mountains of documentation like a System Security Plan (SSP), and a precise method for collecting evidence that will hold up under an auditor's scrutiny.
Practical Reality: Think about the time your team would have to pull from your core business operations. They'd be stuck trying to decipher complex government controls, draft policies from scratch, and inevitably fix mistakes along the way. Partnering with a compliance expert prevents those costly missteps and dramatically shortens your timeline to certification, giving you a much better return on your investment.
What Happens if We Fail Our Official CMMC Assessment?
Failing your official CMMC assessment means you'll be locked out of winning or even working on DoD contracts that require that certification level. It's as simple as that. The assessor, known as a C3PAO, will give you a report that details exactly which controls you failed.
From there, you'll have a limited window to fix the problems and will have to pay for a completely new assessment. This is exactly why a "readiness review" with a compliance service is so crucial. It’s the dress rehearsal that lets us find and fix any gaps before the official auditors ever walk in your door, making sure you pass on the first try.
Does Hiring a Service Guarantee We Will Pass the Audit?
No reputable firm can ever offer a 100% guarantee, because the final stamp of approval comes from the independent C3PAO. However, working with an experienced CMMC compliance service puts the odds firmly in your favor. A good partner brings the expertise, a proven process, and the right documentation templates to make sure every box is checked.
We prepare you, your systems, and your team for what's coming. The goal is to eliminate any surprises and make the official audit feel like just another day at the office.
Navigating CMMC isn't just about compliance; it's a critical investment in your company's future. The team at Cyberplex Technologies LLC has the local expertise and a proven process to guide your North Carolina business through every step of the journey. Contact us today to schedule your CMMC readiness consultation.



