A client walks into your office, pulls out a phone, and asks for the Wi Fi password.
That moment feels routine. In a lot of Henderson offices, it still gets handled the same way. Someone hands over the main wireless password, or points to a sticky note on the front desk, and moves on.
For a regulated business, that's one of the easiest ways to create a security problem you won't see until later. The guest device may be clean, or it may be outdated, infected, jailbroken, shared, or already connected to risky networks all week. In 2026, mobile devices account for 92.3% of all WiFi connection requests globally, and the average mobile user connects to 4.7 unique WiFi networks per week, up 19% from 2023, according to WiFi usage statistics compiled here. That matters because every guest device arrives with a different trust level, and none of them should land on the same network your staff uses for email, file shares, VoIP, printers, or line-of-business systems.
A proper guest wi fi network solves a practical problem. It gives visitors internet access without giving them a path into your business.
That distinction matters more in finance, legal, public safety, property management, and manufacturing than it does in a casual retail setting. If your office handles client files, payment data, tenant information, incident records, body cam exports, accounting systems, or Microsoft 365 access, your wireless setup isn't just about convenience. It's part of your risk surface.
Why Your Business Needs More Than Just a Wi‑Fi Password
A password alone doesn't separate trust zones. It only controls entry to whatever network that password protects.

The common mistake in small offices
A law office might have a conference room for clients. A property management firm might have vendors in and out all day. A public agency may host contractors, visiting staff, or interview candidates. In each case, someone needs internet access for an hour or two.
What often happens instead is this:
- Front desk shares the office SSID: Guests join the same wireless network employees use.
- Printers and PCs stay visible: Devices that should never be reachable from guest hardware become discoverable.
- Bandwidth gets contested: Streaming, large updates, and cloud backups from unmanaged devices compete with your business traffic.
- Accountability disappears: When everyone uses the same network, it's harder to explain who connected, when they connected, and what controls were in place.
That last point matters during compliance reviews. If you're expected to show that public or visitor traffic is isolated from internal resources, "we use a password" isn't a serious control.
A guest network is a security boundary
The right way to think about a guest wi fi network is simple. It's not a courtesy feature. It's a boundary.
A secure guest network keeps a visitor from reaching your staff laptops, your copier, your NAS, your security cameras, your VoIP system, or the workstation used to access banking portals and case files. It also protects your employees from the accidental habit of connecting unknown devices to the same digital space as your internal operations.
Practical rule: If a person doesn't need access to your business systems, their device shouldn't be able to see your business systems.
That applies even when the visitor is trusted. Contractors, vendors, interview candidates, and clients aren't threats by default. But their devices are still unmanaged from your point of view.
Policies matter too
A solid guest setup should also line up with written expectations. If you haven't documented what's allowed on company internet connections, review your acceptable use policy guidance and make sure guest access rules don't conflict with employee rules, filtering standards, or compliance requirements.
A clean policy usually covers:
- Who can request access
- What activities are blocked
- How long access lasts
- Whether traffic is logged
- Who approves exceptions
That's the operational side many businesses skip. They build Wi Fi, but they don't define how it should be used.
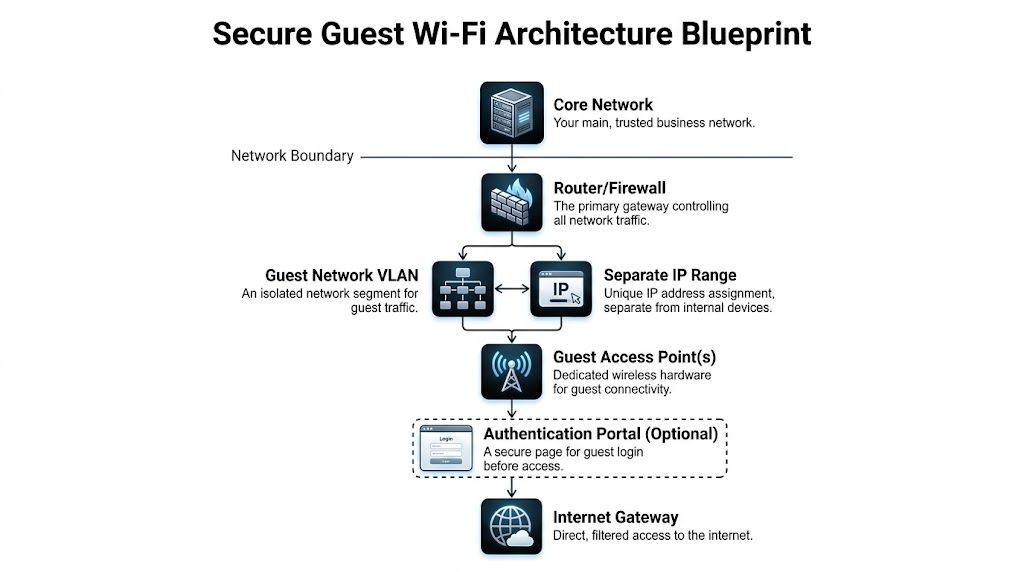
Designing Your Secure Guest Wi‑Fi Architecture
A secure wireless design starts before anyone clicks "enable guest network" in a router interface.
The architecture has to do one thing well. It must keep guest traffic on a separate path from business traffic, while still letting guests reach the internet reliably.
Think in lanes, not passwords
The easiest way to explain this to a business owner is with lanes on a highway.
Your core network is the private lane. That's where employee laptops, line-of-business servers, printers, storage, phones, and management systems live. Your guest network needs its own lane, with controlled entry and no crossover into the private lane.
That separation usually depends on two building blocks:
- SSID: The name guests see when they connect to Wi Fi.
- VLAN: The network segment underneath that SSID that keeps traffic separated.
If you only create a second Wi Fi name without separate segmentation, you haven't built real isolation. You've created two doors into the same room.
What good segmentation looks like
A proper guest wi fi network should include these design choices:
- Dedicated guest SSID: Visitors connect to a clearly labeled guest network, not the staff wireless.
- Separate VLAN and subnet: Guest traffic is placed on its own logical network.
- Firewall rules: Guests can reach the internet, but not internal devices or management interfaces.
- Client isolation: One guest device shouldn't be able to talk directly to another guest device.
- Filtered DNS and web access: Risky traffic gets blocked before it turns into a problem.
- Logging: The network records enough detail to support review, troubleshooting, and compliance.
According to segmentation guidance summarized here, properly segmenting guest traffic with a dedicated VLAN and enabling client isolation can reduce the success rate of lateral movement attacks by over 85%.
That's why segmentation isn't optional. It's the control that makes the rest of the guest network meaningful.
What doesn't work
Businesses often assume one of these shortcuts is "good enough." It usually isn't.
| Shortcut | Why it fails in practice |
|---|---|
| Different password on same network | Guests still share the same trust zone as staff devices |
| Consumer router guest mode with no testing | Settings may exist, but isolation may be incomplete or inconsistent |
| Separate access point with no firewall policy | New hardware doesn't help if traffic still routes into internal resources |
| Open Wi Fi with posted password nearby | Access control is weak and accountability is poor |
The point isn't to buy the most expensive gear. The point is to verify that your router, firewall, switches, and access points can enforce the separation you think you have.
Design for your actual business workflow
A finance office has different needs than a coffee shop. A sheriff's satellite office has different needs than a property manager with a leasing lobby. That's why the design should reflect how your people and visitors use the space.
For many SMBs, the right pattern is:
- Staff network for business devices only
- Guest network for visitors and unmanaged devices
- Optional third segment for IoT or facilities devices
That third segment matters more than people expect. Smart TVs, door controllers, cameras, and conference room appliances shouldn't share space with either guests or employee workstations.
If you want a deeper look at segmentation strategy for small organizations, this practical guide to network security for small business in 2026 covers the broader planning approach around network boundaries, access, and monitoring.
Good guest Wi Fi design feels boring once it's done. That's the goal. Visitors get internet, employees work normally, and nothing crosses lines it shouldn't.
Step-by-Step Guest Network Configuration
Once the design is right, configuration gets much easier.
Most business-grade firewalls, wireless controllers, and access points follow the same general pattern even if the screens look different.

Start with the gateway, not the access point
The first mistake I see is building the guest SSID at the wireless layer before the gateway or firewall is ready.
Start at the edge of the network:
- Log into the router or firewall admin console
- Confirm it supports guest segmentation
- Check firmware status
- Review current LANs, wireless networks, and firewall policies
If the hardware can't create a separate guest network with policy controls, stop there. A cosmetic guest SSID on underpowered hardware isn't a secure setup.
Create the guest network object
In most admin interfaces, you'll find an area for networks, interfaces, or VLANs. Create a dedicated guest network and label it clearly.
Use naming that people can understand at a glance:
- OfficeName Guest
- Lobby Guest
- Visitor Wi Fi
Avoid names that reveal your firewall brand, internal naming convention, or location details that don't help the user.
At this stage, define the guest network as isolated from your production LAN. The exact menu may say guest VLAN, separate interface, isolated SSID mapping, or network segmentation.
Build the guest SSID carefully
Now create the wireless network itself.
Your guest SSID should usually be:
- Broadcasted on 2.4 GHz and 5 GHz for broad compatibility
- Mapped only to the guest segment
- Separated from staff SSIDs by policy
- Easy to recognize at reception
For security settings, use WPA3 where your environment supports it, with fallback planning if you still have a mixed device population. Don't leave encryption off for convenience.
A strong guest password doesn't need to be impossible to type. It needs to be controlled, rotated, and separated from employee credentials.
Good examples usually share these traits:
- Long enough to resist guessing
- Not reused from your staff Wi Fi
- Not based on business name alone
- Changed on a schedule or after sensitive events
Turn on client isolation
This setting may be labeled client isolation, AP isolation, station isolation, or something similar.
Enable it.
That prevents one guest device from directly reaching another device on the same guest wireless network. In real life, this matters when multiple visitors are in a lobby, conference room, waiting area, or training event.
A guest network without client isolation is much easier to abuse for local scanning, peer attacks, or accidental device discovery.
Add firewall rules that match the design
This is the part people skip because the Wi Fi appears to work before the rules are finished.
The firewall should explicitly allow guest users to reach the internet while blocking access to:
- Internal file shares
- Printers
- Server networks
- Phone systems
- Camera networks
- Management interfaces
- Other private segments
Don't rely on assumed defaults. Review the actual rule set and test it.
After configuration, connect a test device to the guest SSID and try to reach internal resources. The correct result is failure.
Validate with a real test routine
A quick "it gets online" check isn't enough.
Use a practical test list:
- Join the guest SSID from a phone
- Browse public websites
- Confirm captive portal behavior if enabled
- Try to discover local printers or internal hosts
- Check whether one guest device can see another
- Run a basic speed test
- Make sure staff applications still perform normally
The walkthrough below is useful if you want to compare your interface against a live example before making changes:
Keep the configuration simple enough to support
A guest wi fi network fails when no one can explain how it works six months later.
Document these items before you leave the project:
| Configuration item | What to record |
|---|---|
| SSID name | Exact guest wireless name |
| Security mode | WPA setting and password rotation process |
| Segmentation | Which guest network maps to which isolated segment |
| Firewall intent | What guests can access and what they can't |
| DNS and filtering | Which protections are applied |
| Support process | Who changes passwords, reviews logs, and troubleshoots issues |
If your documentation only says "guest Wi Fi enabled," you don't have documentation. You have a vague memory.
Implementing Authentication and Access Controls
A guest wi fi network shouldn't be equally open to everyone at all times.
Once the network exists, the next job is controlling access in a way that fits your business. A law office may want simple password access at reception. A property manager may prefer a portal with terms of use. A hospitality venue may want a smoother login flow because customer experience directly affects time on site.
Guest WiFi analytics show that 70% of restaurant patrons prefer venues with hotspots, and 67% of users report staying longer, by an average of 23 minutes, when free WiFi is available, according to guest WiFi analytics data summarized here. Even if you're not in hospitality, the lesson applies. Access design changes behavior.
Pick an access model you can manage
The best authentication method isn't the fanciest one. It's the one your staff can support without workarounds.
Here is a practical comparison.
| Method | Best For | Security Level | User Experience |
|---|---|---|---|
| Shared password | Small offices with limited guest volume | Moderate if rotated regularly | Easy for visitors, easy for staff |
| Captive portal with terms acceptance | Professional offices and public-facing lobbies | Moderate to strong depending on controls | Familiar, adds one extra step |
| Reception-issued temporary credentials | Regulated businesses and frequent contractor visits | Stronger control and better accountability | Slightly slower, but more controlled |
| Social login | Marketing-focused venues | Lower fit for regulated offices | Fast for users who don't mind sharing profile data |
Where each method works
Shared password
This is the easiest option to run.
It works well when guest traffic is light and reception can hand out the password directly. The catch is operational discipline. If the password never changes, vendors and former visitors may still know it long after they should.
Use it if your business wants simplicity, but tie it to a rotation schedule.
Captive portal
A captive portal places a login or acceptance page between the guest and the internet.
This is often the best middle ground for SMBs because it lets you present terms, display usage rules, and optionally require a password. It also helps you standardize the guest experience across different device types.
Temporary credentials
For accounting firms, legal offices, municipal sites, or environments with recurring vendors, temporary credentials are cleaner.
Reception or an administrator can issue time-limited access rather than sharing one standing secret with everyone. That reduces the spread of persistent passwords and gives you more confidence about who was on the network.
Control session time and bandwidth
Authentication is only one side of access control. The other side is limiting what a guest session can consume.
Good guest controls usually include:
- Session timeout: Disconnect users after a defined period so access doesn't linger indefinitely.
- Idle timeout: End stale sessions when a device is no longer active.
- Bandwidth limits: Keep one heavy user from degrading the experience for everyone else.
- Application priority: Protect VoIP, Microsoft 365, and business apps from guest traffic spikes.
If your staff relies on softphones, Teams calls, or cloud accounting platforms, bandwidth control isn't optional. A guest watching video in the lobby shouldn't affect a client call at the front desk.
Add terms that match your environment
A portal page is also a policy tool.
Use plain language that tells guests:
- The network is for internet access only
- Activity may be logged
- Illegal or abusive use is prohibited
- Access can be revoked
- The business isn't responsible for unsecured personal devices
That's not just legal housekeeping. It helps staff answer challenges consistently when someone asks for unrestricted access or objects to filtering.
Put filtering and enforcement at the firewall
Wireless settings get people connected. The firewall decides what connected users can do.
For that reason, guest controls should align with your perimeter security policies. If you need stronger oversight of filtering, inspection, and outbound control, this guide to managed firewall service in 2026 is useful because guest access is only as safe as the rules behind it.
One practical option for Henderson-area regulated SMBs is to manage guest access through a segmented firewall policy and monitored wireless stack, whether that is handled internally or through a provider such as Cyberplex Technologies LLC. The important part is consistency. Authentication, filtering, logs, and bandwidth rules should all support the same security model.
Guests don't need "full internet." They need appropriate internet, on a network that can't interfere with business operations.
Advanced Hardening and Proactive Monitoring
Many businesses stop once they enable guest mode, set a password, and check the box for isolation.
That baseline is better than nothing. It still isn't enough for firms with compliance pressure, sensitive data, or a low tolerance for operational risk.

Default guest settings can fail under real attack conditions
A common assumption is that client isolation solves guest-to-guest risk once and for all.
Recent security research exposed flaws in WPA2/WPA3 client isolation on popular router firmware, showing that techniques like AirSnitch can bypass protections that many admins assumed were reliable, as described in this report on guest network isolation flaws. That doesn't mean guest networks are pointless. It means they need layered defenses instead of blind trust in one feature.
What to add beyond the basics
A hardened guest wi fi network usually includes several controls working together.
DNS filtering
This is one of the most practical upgrades because it doesn't depend on controlling guest devices directly.
Filtered DNS can block known malicious domains, phishing destinations, command-and-control lookups, and risky categories before the connection gets far. For unmanaged devices, that's useful because you often can't install endpoint tools or certificates.
Logging that people actually review
Logging should capture enough information to answer practical questions:
- Which device connected
- When it connected
- Which SSID it used
- How long the session lasted
- Whether the device triggered blocked requests
- Whether unusual traffic patterns appeared
Logs nobody reviews are only slightly better than no logs. Set alerts for behavior that deserves human attention, such as repeated blocks, unusual scanning behavior, or suspicious spikes in outbound requests.
Firmware discipline
Guest Wi Fi security depends partly on the wireless and gateway firmware staying current.
If your access point or firewall hasn't been updated in a long time, your configuration may look good while the underlying platform remains exposed. This is especially important if you're relying on guest mode features built into small-business or prosumer hardware.
Add controls for regulated offices
If you're in finance, legal, or public safety, I recommend thinking in layers, not settings.
A stronger stack typically includes:
- Segmentation at the firewall
- Client isolation at the wireless layer
- DNS filtering for guest egress
- Web category controls where appropriate
- Alerting on suspicious guest behavior
- Retention of logs for review and audits
- Periodic validation that isolation still works after updates
A secure guest network isn't one feature. It's a chain of controls. Attackers only need one weak link.
Test the assumptions, not just the signal strength
A lot of businesses test coverage and speed. Fewer test security boundaries after changes.
Whenever you replace an access point, update firmware, change internet providers, or alter firewall policy, retest the guest network. Confirm that visitors still can't reach internal resources and that filtering, timeouts, and logging behave the way you intended.
That's the difference between a setup that looked secure on install day and one that stays secure under day-to-day change.
Your Operational Checklist and Troubleshooting Guide
A guest wi fi network isn't a one-time project. It's an operational system.
For regulated industries, failing to properly log and monitor guest Wi-Fi traffic can lead to audit failures under standards like PCI-DSS or HIPAA, and post-2025 data shows a 40% rise in SMB ransomware originating from guest network vectors, according to guest WiFi security best practices discussed here. That means your long-term process matters just as much as the original build.
Weekly and monthly checklist
Use a simple operating rhythm. The exact owner may be internal IT, an office manager, or an MSP, but someone should be accountable.
Weekly checks
- Review recent guest activity: Look for unusual usage patterns, repeated failed logins, or blocked destinations that suggest abuse.
- Confirm staff performance: Ask whether VoIP calls, cloud apps, or file access slowed down during guest-heavy periods.
- Test access from one guest device: Make sure internet access works and internal resources still remain unreachable.
Monthly checks
- Rotate the guest password if you use a shared credential: Especially after events, contractor turnover, or public exposure.
- Review firewall and filtering policies: Confirm rules still reflect current business needs.
- Check firmware status on firewall, switches, and access points: Don't let known issues linger because the network seems quiet.
- Audit captive portal content: Terms, branding, and legal language should still be accurate.
- Verify logging retention: Make sure logs are available for troubleshooting and compliance review.
Quarterly checks
- Run a segmentation validation test: Confirm guests still can't access printers, internal shares, management pages, or staff devices.
- Review device inventory near the guest environment: New smart TVs, conference appliances, and building tech often appear without anyone thinking about segmentation.
- Reassess bandwidth policy: Visitor traffic patterns change over time. Your limits may need adjustment.
What to document for compliance
If your business is ever asked how guest access is controlled, you should be able to answer without guessing.
Keep these records current:
| Item | Why it matters |
|---|---|
| Guest SSID details | Shows which wireless network is designated for visitors |
| Access method | Documents whether you use password, portal, or temporary credentials |
| Segmentation notes | Demonstrates that guest traffic is isolated from internal systems |
| Logging and retention process | Supports incident review and compliance questions |
| Change history | Helps explain what changed after outages or audits |
| Assigned owner | Makes support and accountability clear |
Troubleshooting the issues people actually report
Most guest Wi Fi tickets fall into a handful of categories.
Can't see the guest network
Check whether the SSID is being broadcast on the expected radios and whether the nearest access point is online. If only some users can't see it, the issue may be device compatibility rather than a full outage.
Connected but no internet
This usually points to one of three problems. The guest VLAN may not have proper internet egress, the firewall rule may be too restrictive, or DNS filtering may be misconfigured. Test from a known-good device before changing policy.
Stuck on the login page
Captive portals can fail when sessions get cached, pop-up windows are blocked, or DNS redirection behaves inconsistently. Have the user disconnect, forget the network, reconnect, and reopen a standard browser.
Internet is slow
Check whether a few users are saturating the guest bandwidth pool or whether the ISP connection is under pressure overall. Also confirm that guest QoS is still deprioritized behind business traffic.
Guest can reach something internal
Treat this as a security issue, not a convenience problem. Disconnect the guest SSID if necessary, review the mapped network segment, and verify firewall rules line by line. Don't assume the cause is minor.
A simple ownership model works best
Many SMBs overcomplicate support by splitting responsibility across office staff, vendors, and whoever last touched the firewall.
A cleaner model is:
- One owner for password and user-facing issues
- One owner for firewall and segmentation changes
- One documented process for emergency disablement
- One review cadence for logs, firmware, and policy
That approach reduces finger-pointing when something breaks.
The best guest Wi Fi network is the one your team can operate calmly, document clearly, and trust during an audit.
If your Henderson-area business needs a guest wi fi network that supports compliance, protects internal systems, and won't create support headaches later, Cyberplex Technologies LLC can help you assess your current setup, segment traffic correctly, and put monitoring and controls in place that fit the way your office works.



