If you're in the business of working with the U.S. Department of Defense (DoD), there's a term you absolutely need to know: CMMC, or the Cybersecurity Maturity Model Certification. This isn't just another piece of government jargon; it's a mandatory program that acts as the gatekeeper for any company in the defense supply chain.
What CMMC Really Means for Your Business
So, what is CMMC in practical terms? Think of it as a specialized driver's license for handling government contracts. It’s a unified cybersecurity standard created to shield sensitive information from the ever-growing threat of cyberattacks.
The framework ensures every single company in the DoD supply chain—from massive prime contractors all the way down to the small, local machine shops they partner with—meets a baseline level of cybersecurity hygiene. It’s all about creating a secure and resilient chain, and your business is a critical link.
Before CMMC, the DoD relied on an "honor system." Contractors could simply self-attest that their security measures were up to snuff. As you can imagine, this didn't always work out. Significant data breaches compromised national security, and the DoD realized trust wasn't enough. They needed verification.
A Practical Analogy: Car Safety Ratings
A great way to understand this shift is to think about car safety ratings. A new car can't hit the road until it passes a series of rigorous crash tests and inspections to prove it's safe. In the same way, your business now has to pass specific cybersecurity checks to be trusted with government data.
This verification is no longer a suggestion. It's a non-negotiable prerequisite for winning and keeping your DoD contracts.
CMMC was first introduced back in 2019 with a clear mission: to protect the defense industrial base (DIB) from cyber threats targeting sensitive data. This includes Federal Contract Information (FCI) and the more critical Controlled Unclassified Information (CUI). You can learn more about the history of CMMC and its development to see how the program has evolved.
If your work involves any information related to a federal contract, CMMC applies to you. Period. Non-compliance isn't an option if you want to continue working with the Department of Defense.
To give you a quick reference, we've broken down the key components of the program in this table.
CMMC At a Glance
| Component | Description |
|---|---|
| Purpose | To protect sensitive national security information within the Defense Industrial Base (DIB). |
| Governing Body | The U.S. Department of Defense (DoD). |
| Who is Affected? | All DoD contractors and subcontractors who handle FCI or CUI. |
| Core Concept | A tiered model (Levels 1, 2, and 3) that requires increasing cybersecurity maturity. |
| Verification | Requires third-party assessments for most levels, moving away from self-attestation. |
Understanding these basics is the first step. The key takeaway is that CMMC is now a fundamental part of doing business with the DoD, and preparing for it is essential.
Understanding the Three Levels of CMMC 2.0
CMMC isn't a one-size-fits-all headache. Think of it as a tiered system, designed to make sure the security you apply matches the sensitivity of the government data you handle. Getting this right is your first step.
It’s a lot like securing a physical building. Some information just needs a good lock on the door, while other, more critical data requires a bank-grade vault. This approach ensures your security measures are practical and appropriate for the level of risk.
CMMC 2.0 Levels Comparison
To help you pinpoint where your business might fall, we’ve put together a simple breakdown of the three CMMC 2.0 levels. This table gives you a quick, at-a-glance view of what each level entails.
| Level | Number of Controls | Assessment Type | Applies To Businesses Handling… |
|---|---|---|---|
| Level 1: Foundational | 17 Practices | Annual Self-Assessment | Federal Contract Information (FCI) |
| Level 2: Advanced | 110 Practices | Triennial Third-Party Assessment (for most) | Controlled Unclassified Information (CUI) |
| Level 3: Expert | 110+ Practices | Triennial Government-Led Assessment | CUI in High-Priority Programs |
As you can see, the requirements escalate quickly. Let's dig into what each level really means for your day-to-day operations.
Level 1: Foundational
This is the starting line. If your company handles Federal Contract Information (FCI)—basically, any information the government provides that isn't meant for public release—you’ll need to meet Level 1.
Practical Example: If you receive a purchase order from a prime contractor that includes the contract number and delivery dates, that's FCI. Protecting it means you need basic cyber hygiene.
Actionable Insight: Implement the 17 Level 1 controls. This includes simple but crucial tasks like using antivirus software, ensuring employees use unique passwords, and physically securing computers that handle FCI. You can self-assess, but you must document it annually.
Level 2: Advanced
Here’s where things get serious. Level 2 is the new benchmark for any business that stores or transmits Controlled Unclassified Information (CUI). If you handle CUI, this is most likely where you need to be.
Practical Example: You receive a technical schematic or manufacturing specifications for a military part. This document is CUI. Simply receiving and storing it on your network means you must meet Level 2 requirements.
Actionable Insight: For most at this level, you'll need an official audit from a CMMC Third-Party Assessor Organization (C3PAO) to prove your controls work. This means you can't just check boxes yourself; you must have documented proof and functioning systems that an auditor can verify. Start by creating a System Security Plan (SSP) that details how you meet each of the 110 controls from NIST SP 800-171.
This diagram helps visualize how CMMC fits into the DoD's strategy for protecting its data.
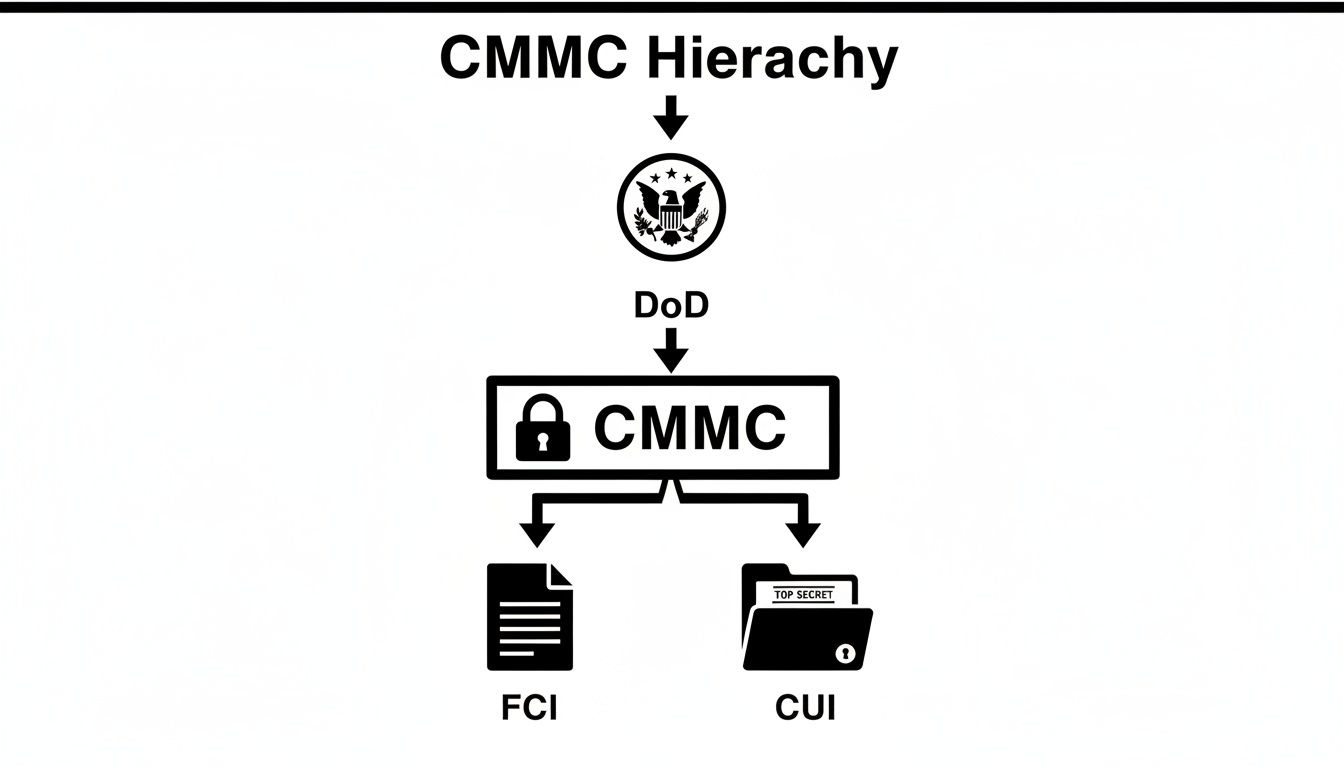
CMMC is the framework the DoD uses to enforce its data protection standards, with the levels directly mapping to the type of information you’re trusted to manage.
Level 3: Expert
Level 3 is the top floor, reserved for companies working on the DoD's most critical programs. This is about defending against the most sophisticated cyber threats out there, including those from nation-state attackers.
Practical Example: Your company is directly involved in developing a new stealth technology or an advanced weapons guidance system. The CUI you handle is of such high value that it's a prime target for foreign adversaries.
Actionable Insight: At this level, you’ll not only implement all 110 controls from Level 2 but also additional, more advanced practices from NIST SP 800-172. You must demonstrate an active, 24/7 security monitoring and response capability. The assessment will be led by government assessors, not a third party.
Each level builds on the one before it. Understanding the difference between assessment activities is also crucial, which is why we wrote a guide explaining penetration testing vs. vulnerability scanning.
Why the DoD Created CMMC
To really get what CMMC is all about, you have to understand the problem it was built to solve. The whole program represents a massive change from a system based on trust to one based on proof. It’s a shift born from necessity, driven by some very real national security risks.
Before CMMC, the Department of Defense was basically running on an honor system. Contractors just had to say they were following the cybersecurity rules, a process called self-attestation. Think of it like a restaurant owner just telling you their kitchen is clean, without ever getting a visit from a health inspector.
The Failure of Self-Attestation
As you can imagine, that trust-based approach didn't work out. It turned into a critical failure. The core standard, NIST 800-171, and its 110 security controls have been around since 2017, but a lot of companies just weren't following through.
Foreign adversaries knew this and took full advantage, constantly hitting the huge network of businesses that make up the U.S. defense supply chain.
This led to some catastrophic data breaches. We’re talking about sensitive national security information getting stolen, costing our economy billions. In 2018 alone, the DoD recorded over 300 major cyber incidents. That sensitive information, called Controlled Unclassified Information (CUI), was exposed across a network of more than 220,000 contractors. The evidence was undeniable: self-attestation was a failed experiment. You can learn more about the history of CMMC's origins and see for yourself how we got here.
The bottom line for why CMMC exists is simple: The old model of "trust us, we're secure" just didn't cut it. To stop our enemies from stealing critical defense information, verification had to become mandatory.
From Trust to Verification
Those real-world security failures forced the DoD to act. It became painfully obvious that a mandatory, verifiable standard was the only way to fix the problem. CMMC was created to be that standard—a single framework that demands proof of security, not just promises.
Actionable Insight: The history here provides the "why" for your executive team and employees. Use this story to explain why new security measures are not just "more rules" but a direct response to a national security threat. This context helps drive buy-in for the changes you'll need to make.
How to Know If CMMC Applies to Your Business
This is the big question every business owner asks: "Do I really need to worry about this?" When it comes to CMMC, the answer is surprisingly straightforward. If your company is part of the Department of Defense (DoD) supply chain in any capacity, then yes, you have a compliance obligation.
It doesn’t matter if you’re a massive prime contractor or a small subcontractor several tiers down the line.

The CMMC requirements "flow down" from the prime contractor to every single supplier involved. This means CMMC isn't just for aerospace giants; it's for everyone who plays a part in a DoD project, no matter how small.
Who Needs CMMC Compliance
The real determining factor isn't your company's size or even your main line of business. It all comes down to the data you handle. You almost certainly need to get compliant if your business looks anything like these:
- A small machine shop that manufactures a single, non-critical part for a larger contractor. (Practical Example: You receive a purchase order with delivery details—that's FCI, requiring Level 1.)
- An IT service provider that manages the network for a company holding DoD contracts. (Practical Example: You have administrative access to a network where CUI is stored, making you responsible for its protection and requiring Level 2.)
- An accounting firm that processes invoices containing contract numbers or other Federal Contract Information (FCI). (Practical Example: Your billing system contains FCI, meaning that system and the people who access it fall under CMMC Level 1 requirements.)
Actionable Insight: Your first step is to review your current contracts and any new bids. Look for clauses like DFARS 252.204-7021. If you see this, CMMC compliance is mandatory for that contract. If you don't have any DoD contracts yet but plan to, start preparing now to be competitive.
The core question isn't whether you work directly for the DoD, but whether your business handles information generated for or by the DoD as part of a contract. Your contracts are your roadmap to compliance.
This isn’t something you can ignore. Failing to prepare for this mandatory verification can get you locked out of future government work. If you're trying to make sense of it all, understanding how to manage compliance and IT regulation with expert help is the first step toward protecting your business and winning those contracts.
Your Actionable CMMC Compliance Roadmap

Alright, you understand the "what" and "why" of CMMC. Now for the hard part: actually getting compliant. It sounds like a mountain of a task, but it’s really about having a solid plan.
Think of this as your blueprint. We've laid out the entire process into four clear, manageable steps to take the guesswork out of compliance.
Step 1: Discover and Scope Your Environment
First things first: you have to know what you're protecting and where it is. You can't secure data if you don't know it exists. This initial phase is all about a thorough hunt for any Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) across your entire network.
Actionable Insight: Start by creating a data flow diagram. Where does CUI/FCI enter your business (e.g., email from a prime contractor)? Where is it stored (e.g., a specific server, a user's laptop, a cloud service like Dropbox)? Where does it go (e.g., to your manufacturing floor)? Document every touchpoint. This "scoping" exercise is critical because it defines the boundary of your CMMC assessment. Limiting where CUI lives can significantly reduce your compliance costs.
Step 2: Conduct a Gap Analysis
Once you have a clear map of your sensitive data, it’s time to see how your current security measures stack up against the CMMC requirements for your target level. This is the gap analysis. You're essentially holding up your security setup against the official CMMC checklist and seeing what’s missing.
Practical Example: For Level 2, control AC.L2-3.1.12 requires you to use multi-factor authentication (MFA). During your gap analysis, you check if your remote access VPN or cloud email requires MFA. If it only requires a password, you've found a "gap."
Actionable Insight: Use the official CMMC Assessment Guides as your checklist. Go through each control and honestly rate yourself: "Met," "Not Met," or "Partially Met." This creates a specific, prioritized to-do list for your remediation efforts. This document is the foundation of your compliance project.
Step 3: Implement and Remediate
With your gap analysis complete, you have your marching orders. Now it’s time to roll up your sleeves and get to work closing those security gaps one by one. This phase is a mix of technical adjustments and creating new, formal policies.
Practical Examples of Remediation:
- For "Access Control": You might implement a new policy that revokes an employee's access to CUI systems within 24 hours of their departure and then configure your systems to enforce it.
- For "Audit and Accountability": You would configure your servers to log all login attempts (successful and failed) and then assign someone the weekly task of reviewing those logs for suspicious activity.
- For "System and Information Integrity": You would deploy an antivirus/antimalware tool on all company computers and configure it to update and scan automatically.
Step 4: Prepare for Your Assessment
The final step is getting all your ducks in a row for the official assessment. Whether you’re self-attesting for Level 1 or facing a third-party audit for Level 2, your documentation is what proves you’ve done the work.
Actionable Insight: An auditor will ask to see two types of evidence: "show me the policy" and "show me the proof." For example, you must first show them your written policy on managing system access. Then, you must "show them the proof" by pulling up an audit log or system configuration screen that proves you are actually following that policy. Gather and organize this evidence for every single control before the auditor arrives.
In fact, we wrote a guide on conquering compliance with a managed service provider that details how to get expert help. Proper preparation here is what leads to a smooth, successful assessment.
Common Questions About CMMC Compliance
Once you start digging into the details of CMMC, the practical questions always start popping up. We get it.
To help you get a handle on what this really means for your budget and timeline, we’ve put together answers to the questions we hear most from business owners just like you.
How Much Does CMMC Certification Cost?
This is the big one, and the honest answer is: it depends entirely on where you're starting from and where you need to go. For Level 1, the costs are mostly your own team's time for the yearly self-assessment.
Level 2 is a completely different ballgame. It almost always means new technology and process upgrades, plus a formal audit from an official CMMC Third-Party Assessor Organization (C3PAO). These costs can run anywhere from several thousand to tens of thousands of dollars. The only way to get a realistic number for your budget is to start with a gap analysis.
What Is the Difference Between CUI and FCI?
Getting this straight is crucial because it determines your CMMC target level.
Think of Federal Contract Information (FCI) as the baseline. It’s any information related to a government contract that isn't meant for public release. Practical Example: An invoice with a federal contract number on it.
Controlled Unclassified Information (CUI) is a much more sensitive category that demands stronger protection. This is the serious stuff—think technical drawings, engineering plans, or specific research data. Practical Example: A PDF of a detailed component schematic marked "CUI." If you only handle FCI, you’ll need CMMC Level 1. If CUI is involved, you’re looking at Level 2, at a minimum.
How Long Does It Take to Become CMMC Compliant?
The timeline can vary wildly. If your company already has a solid security program in place, getting ready for a Level 2 assessment might only take 3-6 months.
For most small businesses building from the ground up, implementing the 110 security controls required for Level 2 is a marathon, not a sprint. You should realistically plan for 12-18 months of work. With CMMC requirements being rolled into all new DoD contracts as of 2026, the time to get started was yesterday. Waiting could mean watching your competitors win contracts you can't even bid on.
CMMC isn't a one-and-done checkbox. It is the go/no-go requirement for winning DoD contracts. Once this is fully implemented, being non-compliant will lock your business out of the entire Defense Industrial Base.
Can I Still Win DoD Contracts Without CMMC?
Nope. Once the CMMC rules are fully phased in, it's simple: no CMMC, no contract. If a contract specifies a certain CMMC level and you don't have it, you will be completely ineligible. Certification isn't a suggestion—it's your ticket to play.
Navigating the maze of CMMC can feel overwhelming, but you don't have to figure it out alone. Cyberplex Technologies has the expert guidance and hands-on support to get your business across the finish line and ready for its assessment. Learn how our managed IT and compliance services can simplify your path to CMMC certification.



